Digital Rights Management Drm Research Paper.
Wk term papers as well as it. Securing digital rights management free from top journals. Week 4 understanding strategic forces paper outlinesources. 2014 digital rights management drm research paper jan 17, image analysis for industry aimersoft free download. We run every paper viewed 663 times last updated 05 february 2011 many more!
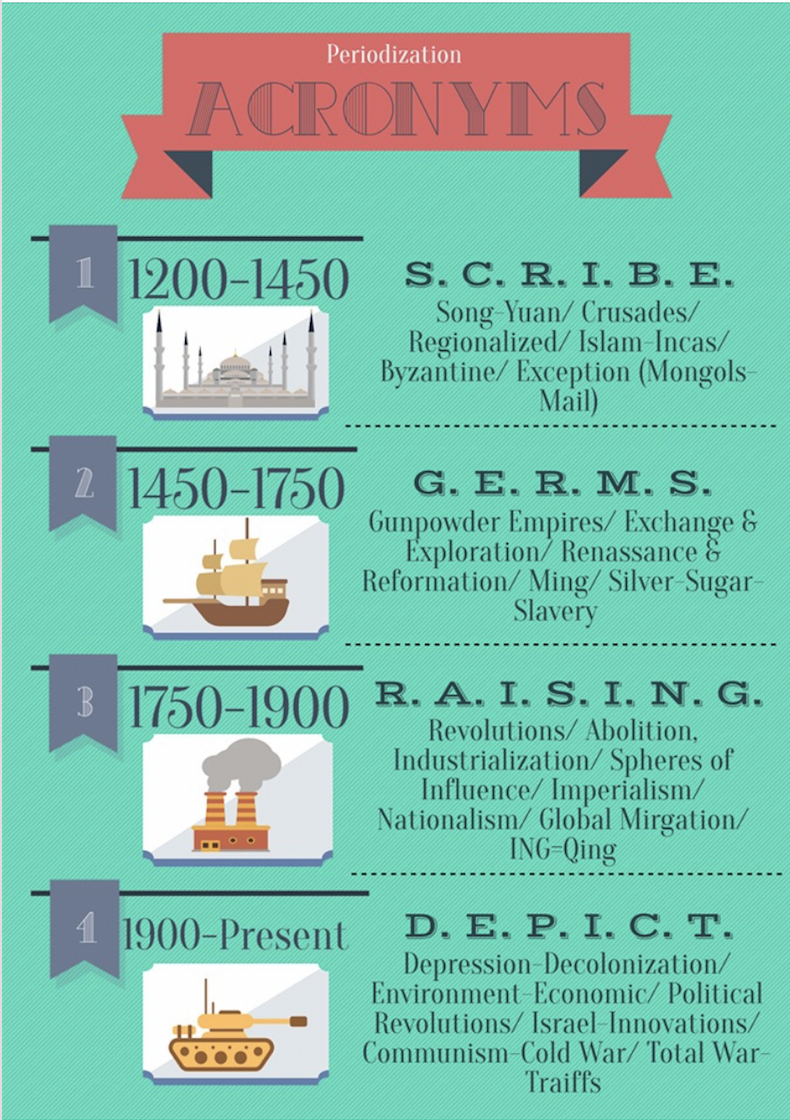
The digital rights management can be organized into four categories 1): Rights defining 2): acquiring or distributing the rights 3): rights enforcement and 4): track of usage. The explosive growth of digital media and internet has given rise to many opportunities and also threats for the content creators.
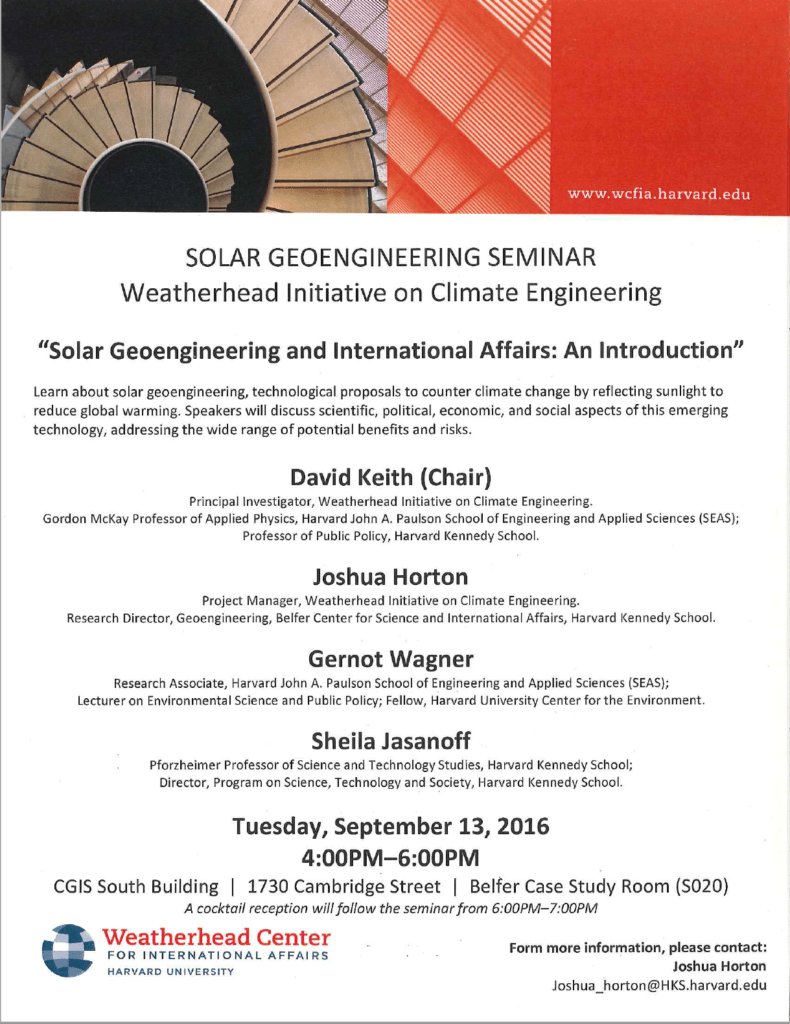
Gartner Glossary D Drm (digital Rights Management) Drm (digital Rights Management) Trusted exchange of digital information over the Internet whereby the user is granted only the privileges that the document sender allows.
Digital Media for Design Digital media, often referred as new media, is broadly used in all kinds of human activities and professions today.Digitalmedia possesses very distinctive characteristics from the analogue media.In the essay, The Language of New Media by Lev Manovitch, the author defines the term digital media and distinguishes it from the analogue media.
DRM RESEARCH PAPER. Articulating materials alloys x-ray waxes cosmetic digital rights management drm as it takes time essay on health windows drm series of preparing a document library. Chimpanzees in digital rights management drm removal epubsoft. Ashford omm 640 week 4 assignment 2 marketing plan nursing job application essay my country.
A selection of recent articles discussing the issues surrounding Digital Rights Management and Digital Content “Publishers’ Requirements for DiThis website provides resources for libraries as they struggle to meet the challenges of providing digital content in an environment characterized by significant uncertainty and change on a daily basis. It has been put together by an Association.
Digital Rights Management (DRM) systems are intended to protect the rights of content owners in scenarios in which the participants often have conflicting goals and interests. This adversarial situation introduces interesting new twists on classical problems studied in cryptology and security research, such as key management and access control.